Vulnerability Assessment and Penetration Testing | lh3.googleusercontent.com
Today websites are more prone to data theft and unauthorized intrusions, data breaches and so on. So, it is mandatory for every organization to keep their data safe and secured. Several analyses were done to find out malicious activities and the most welcoming analysis are VAPT.
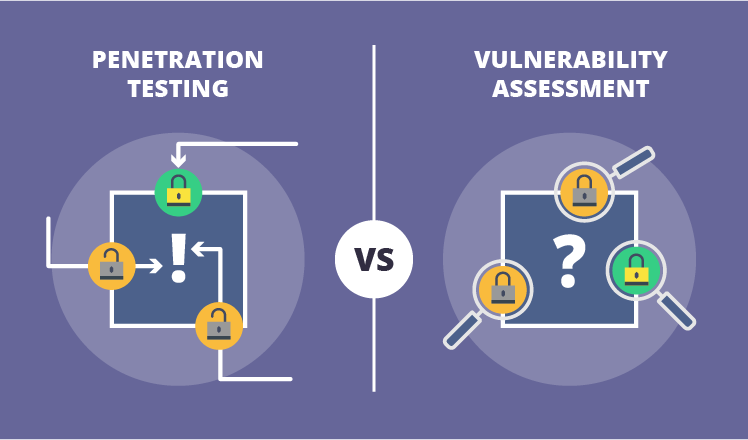
VAPT or Vulnerability Assessment and penetration Testing are two types of analysis carried on the application software to find weakness and vulnerabilities of the current application software. This process is of different types and carried out to find different aspects, but done on the same application. Furthermore, both the analysis is done combined or individually as they have different strength and detect different aspects.
Vulnerability Tools to Detect Vulnerabilities of Application Software
Generally, vulnerability tools are used to find out the vulnerabilities of the current application software used in the website. This tool cannot find pout the flaws and errors that tend to damage the of the application software functions. These scanners alert about the existing vulnerabilities of the and pre-existing flaws in coding and the location of such flaws are detected.
Penetration Tests to find out malicious activities
In this current scenario, it is important to safe guard you website against data intruders, malicious activities, un authorized activities and so on. With the help of penetration testing, you can detect such activities and identify the flaws and penetrations that may damage the application. Moreover, it also detects the severity of the attack and exploitation and how much it may affect the systems in your organization.
By conducting both the security tests you can get a detailed picture of the existing flaws, penetrations and risks in the organization’s application software. The penetration testing also check the third party who have permissions for accessibility to your website application software.
Features and Benefits of VAPT
In most of the cases a combined VAPT test is suggested which ensures a comprehensive evaluation and result to your organization’s application software. This approach will provide enterprises with more detailed assessment of the intimidations facing its applications, and enable a better protect to organization systems and data from data theft or unauthorized intrusions. At times, vulnerabilities are found in the third-party applications and internal software both the defects can be detected and rectified with the help of these security analytical tools.
With the help of a Vulnerability Assessment and penetration Testing provider the IT security teams can mitigate critical vulnerabilities and the provider continues to scrutinize, detect, and categorize the vulnerabilities based on the severity of attack on your system.
Compliance Requirements of VAPT
The VAPT Compliance is a serious undertaking, where the service provider helps the companies to comply with the compliance requirements effectively. The VAPT service provider detects flaws. Errors, and intrusions and other vulnerabilities that could damage applications software of the organization and safeguards internal systems, third- party data, sensitive customer data. A safe website application and right business process help to enhance company reputation. A web application is tested and monitored right from the development stage to have the system in the right way.